DiDi's Troubles, Tweets of the Week (Corruption, Waluigi+Mao, Fish Hugging, Which Chinese Ministry Works the Hardest?)
"The real end of barbarism requires breaking bones and paying a price."
Chinese ride-hailing app Didi Chuxing’s IPO raised $4.4 billion on June 30 in New York. Then everything came crashing down as the Chinese government announced the company would be investigated for data collection and usage violations. China’s cyber watchdog ordered it to halt new user registration and, a couple of days later, Didi was taken off the country’s app stores. In the following week, the rest of the Chinese regulatory universe piled on, with an announced anti-monopoly investigation a particularly worrying development.
According to the chief expert of the Institute of Social Governance at Zhejiang University and founder of the Global Oral History Internet (OHI), Fang Xingdong, the Wild West era for Chinese tech companies has come to an end. As the government shores up data protection, cybersecurity and anti-monopoly laws, the focus is no longer on development but has instead shifted to compliance. And that includes, he argues, addressing the common practice of holding interests outside China.
As Fang writes, this transition won’t be easy. “The real end of barbarism requires breaking bones and paying a price.”
The following piece was translated by Carol Sun, Callan Quinn helped with editing.
Chinese internet companies need to repay a debt of “compliance"
By Fang Xingdong, July 6th, 2021
The Cybersecurity Review Office has recently issued several announcements for internet companies to be reviewed, which has caused great concern. This is new progress in China's efforts to "strengthen anti-monopoly and prevent the disorderly expansion of capital" (one of the eight key tasks that the Central Economic Work Conference has identified for economic work in 2021), as well as to introduce a new measure to implement China's cybersecurity system.
Calls for an end to the brutal growth phase of the internet in China have been around for years. Putting an end to the era of “barbarism” means that in addition to systematic rules and sound institutions, we also need institutions to be in place for the formation of a healthy order. This comprehensive activation of China's network security review mechanism indicates that China's internet enterprises will officially bid farewell to the wild growth stage and establish compliance awareness that will become an important strategy for developing China's internet enterprises.
The Personal Information Protection Law will enter into the third review phase in August and be implemented if no other changes are made. In addition, the Data Security Law will be formally implemented on September 1. The infrastructure construction of the digital era has already taken shape, which also means that the system implementation stage will soon come, namely the compliance stage. Whether laws were not observed in the past or that the law cannot be enforced when everyone is an offender, the superficial development of the internet has passed. In the new stage, internet companies need to truly regard law-based compliance as an important part of sustainable operations.
It is a long and arduous march from the establishment to the implementation of a system.
The Anti-Monopoly Law came into effect on August 1, 2008, but the related penalties in China's internet sector won't come into effect until the end of 2020. It has been more than four years since the Cybersecurity Law came into force on June 1, 2017. Principles around collecting personal information, cybersecurity reviews, and the protection of critical information infrastructure, such as data flow across borders, have been clarified. However, "one or the other", the excessive collection of personal information, big data acquaintance fraud and so on are becoming more and more intense. Institutional implementation is a far more difficult capacity-building project than we can imagine.
The National Security Law, the Cybersecurity Law, the Data Security Law and the Personal Information Protection Law are high-level laws. It is important to complete the legislation, but implementation will be more complex and complicated. Take the operation security of critical information infrastructure, for example, which is the core of the Cybersecurity Law. It involves a series of issues such as the definition, monitoring, defense, disposal, evaluation and review of critical information infrastructure. It requires refinement and detailed rules, a series of bylaws, regulations, and capable supporting mechanisms and departments.
With many users, China's internet giants in the digital age are undoubtedly an important part of the country's cybersecurity. However, they have been allowed to grow wildly.
In addition to longstanding issues such as collecting personal information and the cross-border flow of data, there are also huge pitfalls at the capital level. Almost all of China's internet giants have been driven by venture capital and listed overseas. These companies used a VIE structure, also known as “protocol control", in which an offshore listed entity took control of its onshore business entity. China has restrictions on foreign investment in specific areas such as the internet, news media, education and finance. However, foreign investment bypasses many investments with restrictive policies through the VIE structure and enters almost all areas in China's internet reach.
There is no denying that the VIE structure was an essential contribution to the development of the internet in China. But now, through the VIE structure, shareholders, including the domestic team, and virtually all the interests of internet companies in China are held outside the country. This upside-down situation has undoubtedly become a huge hidden danger in national network security. Therefore, the way these Chinese internet companies get out of the gray area of the VIE structure and move toward a more reasonable and normalized corporate governance structure – which not only meets the needs of national network security, but also is conducive to the financing and listing of enterprises, and continues the open and benign development of the industry – requires the redesign and reconstruction of the overall system.
In short, in the coming years, Chinese internet companies must step out of the comfort zone of their brutal growth in the past and adapt to China's new institutional environment and the basic requirements of internet governance.
Compliance awareness and capability are an important manifestation of risk management for Chinese internet companies and the only way for them to cope with the increasingly complex international environment and seek greater certainty. In the short term, compliance is at the cost of the enterprise, but in the long term, it is an important reflection of its competitiveness.
This is a long-term "debt", but also a “make up lesson”.
Many of the problems with China's internet today are almost entirely caused by the lack of awareness of law and compliance. Especially at the data level, whether it is the collection, processing, use, storage or deletion of all aspects of the whole life cycle, internet enterprises have been free from the system by relying on their monopoly status or the "black box" state of a lack of supervision. The latest round of security review drew back the curtain on China's data security governance and touched the deepest level of China's internet problems.
The system has been established; how to comply with the law is the premise of cybersecurity and the embodiment of the country's governance capacity. Domestic and foreign enterprises are treated equally before the system.
Chinese companies should learn from European and American companies that emphasize compliance and professional competence. The real end of barbarism requires breaking bones and paying a price.
This is what Chinese internet companies should have done, and it is also the only way for Chinese internet companies to build global competitiveness. It is the mission of actively safeguarding national cybersecurity.
Tweets of the Week
If wolf warriors knew what they would be doing this is how they would troll…




Would love a copy of one of these…






Maybe this is the data the government freaked out about?






A thread:

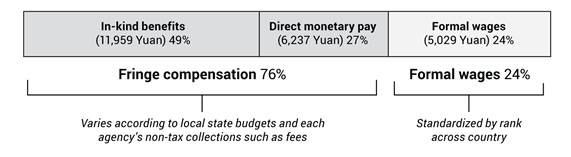



Check out the fantastic podcast episode I recorded with Yuen Yuen on How Corruption Works in China if you haven’t yet.
This one’s from Myanmar.